How Protocols Got Drained
The first quarter of 2026 was brutal for Web3 security. CD Security tracked every protocol-level exploit across the quarter — no scams, no phishing, no rug pulls. Just the technical failures that drained real funds from real protocols.
Here's what the data shows.
📥 Download the full report: Q1 2026 Web3 Exploit Report (PDF)
$169.4M lost across 55 incidents in 90 days
55 protocol exploits. $169.4M gone. And not a single one involved a sophisticated zero-day. Every hack in Q1 2026 exploited known, documented vulnerability classes — the kind that a thorough audit catches before deployment.
January was the worst month by far, accounting for $105.4M of the quarter's total losses. Three incidents — Step Finance ($40M), Truebit ($26.4M), and Matcha ($16.8M) — drove the bulk of the damage.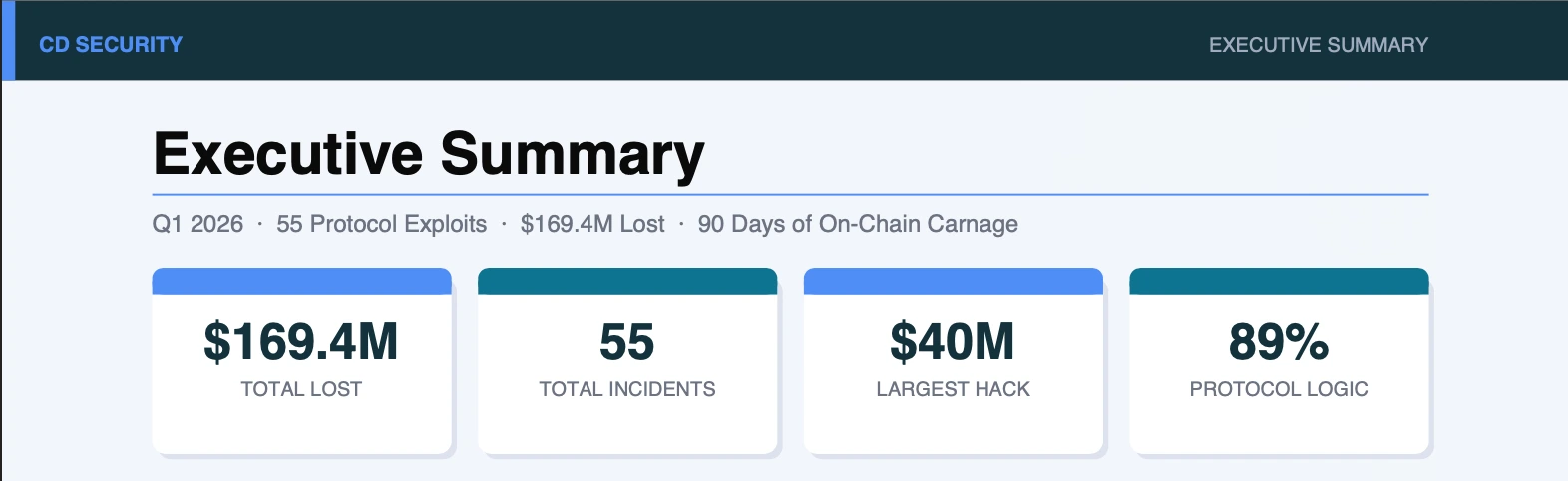
The two categories that matter
Protocol Logic failures drove 89% of incidents. Flashloan-assisted oracle manipulation, deflationary token burn mechanisms weaponized against AMM pools, missing access control on privileged functions, infinite mint exploits. These are not new. They keep appearing because protocols keep deploying unaudited code.
Infrastructure failures — private key and wallet compromises — accounted for only 11% of incidents but caused 43% of total losses. Six incidents, $73.1M gone. Step Finance wound down entirely after losing $40M to a key compromise. Resolv lost $24.5M two months later from the exact same root cause.
The math is stark: infrastructure failures are rare but catastrophic when they happen.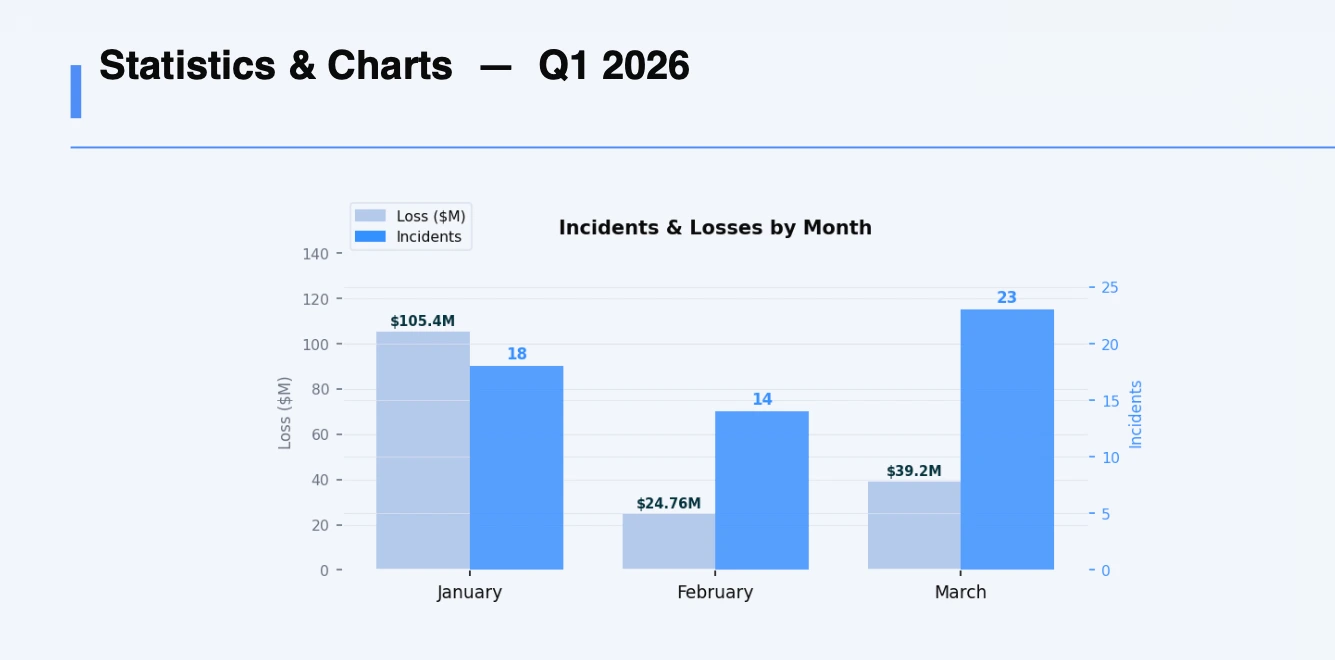
Q1 2026 vs Q1 2025 — what changed
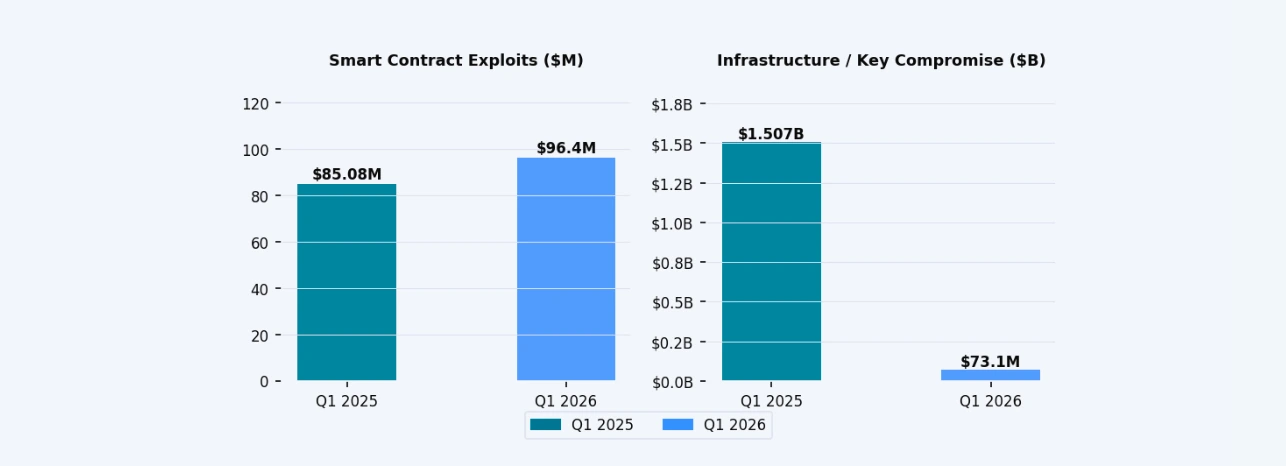
Private key hacks collapsed from $1.507B in Q1 2025 (Bybit alone was $1.46B) to $73.1M in Q1 2026 — a 95% drop. The industry got significantly better at protecting keys.
Smart contract exploits, however, grew 13% year-over-year — from $85M to $96.4M. The attack surface shifted. Blind signing and multisig phishing disappeared. In their place: deflationary token logic exploits, cross-chain message spoofing, and UniswapV4 hook vulnerabilities. New complexity, same root cause.
The three biggest hacks
Step Finance — $40M (January 31). Private key compromise. The protocol announced it was winding down all operations in February as a result.
Truebit — $26.4M (January 8). Bonding curve invariant manipulation. A known exploit class deployed against novel tokenomics without proper economic security review.
Resolv — $24.5M (March 21). Second major private key compromise of the quarter. Two $20M+ infrastructure failures in a single quarter from the same root issue is a signal the industry needs to hear.
What this means for protocol teams
The average loss per Protocol Logic exploit in Q1 2026 was $2.1M. The cost of a quality audit is a fraction of that. Every protocol in this report that got exploited had one thing in common — an unreviewed vulnerability sitting in production.
The full report includes complete incident logs for all 55 exploits, chain breakdown, attack technique analysis, and a Q1 2025 vs Q1 2026 comparison.
📥 Download the Q1 2026 Web3 Exploit Report →
CD Security is a specialized Web3 security firm with over three years of experience auditing smart contracts and protecting high-value protocols across the ecosystem. 150+ completed audits, senior auditors only, start as late as 24h after the request.
Book an audit at cdsecurity.io
