Context
- Accept this before you even start
- Understand why this job pays so well
- Why Web3 security is so attractive
- What the job actually involves
- How long it takes
- The path (detailed)
- Valuable resources (must-save)
- Conclusion
1. What you need to accept before you start
If you want to become a Web3 security auditor, you must accept one uncomfortable truth first.
This is a hard and time consuming game.
Not something you master after one course.
You will feel slow for a long time. You will read code you barely understand. You will miss bugs that feel obvious in hindsight. That is normal. If you are not willing to sit with that discomfort for a long period of time, this path will break you early.
Web3 security rewards people who stay when progress feels invisible.
2. Understand why this job pays so well
Web3 security pays well because mistakes in Web3 are extremely expensive.
A single bug can drain millions of dollars.
A single missed edge case can permanently damage a protocol.
That is why million-dollar bug bounties exist. That is why experienced auditors earn $200k or more per year. Teams are not paying for effort or hours worked. They are paying for someone who can prevent disasters before they happen.
One good finding can save a company more money than an entire engineering team costs in a year.
3. Why is Web3 security so attractive
One reason Web3 security attracts so many people is that the entry requirements are not formal.
You do not need a degree.
You do not need a computer science background.
You do not even need to know how to code on day one.
You can work remotely. You can connect with smart people from all over the world. You can earn very good money. And yes, finding real bugs is genuinely fun. (it gives you that dopamine hit)
But accessibility does not mean ease. If you are not serious about learning and improving every week, the field will quietly filter you out.
4. What the job actually involves
Being a Web3 security auditor is not just about reading Solidity code line by line.
You need to understand how DeFi systems work economically. You need to think like an attacker and constantly ask, “How could this be abused?” You need to understand incentives, user behavior, and edge cases. You also need to communicate clearly with teams, sometimes under pressure.
There is no formal ladder here. If you can find real issues and explain them clearly, people will trust you. If you cannot, no certificate will save you.
Skills you need beyond finding bugs 👇
Finding bugs is the core skill and the main thing you will do, but it is not enough on its own.
You also need:
Clear writing
If you cannot explain a vulnerability clearly, it loses value. Good reports are concise, precise, and actionable. This is a skill you actively practice.
Communication and emotional control
Clients will question findings. Engineers will disagree. You must stay calm, explain your reasoning, and handle pushback professionally. Emotional reactions destroy trust.
Reliability
Audits run on tight timelines. You cannot disappear, miss deadlines, or deliver half-finished work. Being dependable matters more than being brilliant.
Time prioritization
You will never have enough time to check everything. Good auditors know what to ignore and where to focus.
Curiosity
Protocols change fast. Attack techniques evolve. The best auditors constantly ask “what if?” and dig deeper than what is obvious.
Self-direction
No one tells you exactly what to look for. You must decide where to spend your attention and take responsibility for your conclusions.
5. How long it usually takes
There is no fixed timeline.
How fast you progress depends on several things. Prior coding experience helps. A Web2 security background helps even more. Your learning speed matters. So does the amount of time you can dedicate each week.
Some people become strong auditors in one year. Others take two, three, or four years. What matters is not the number of years, but whether you are consistently working on the right things and not getting constantly distracted by other insignificant matters that are catching your attention.
Becoming a decent auditor in about one year is realistic if you focus hard, put in serious time and have burning desire for achieving success in this space.
6. The general path
The overall path is already known. The difficulty lies in execution.
You start by learning how blockchains and smart contracts work.
Then you learn Solidity.
Then you learn security fundamentals.
After that, you spend less time learning and much more time practicing.
Eventually, you start building proof of your skills, and only then do jobs, freelancing, or bounties make sense.
7. Step one: Blockchain and smart contract basics
The BEST starting point is Cyfrin Updraft:
Begin with Blockchain Basics. (6hrs)
Learn how Ethereum works, how transactions are processed, and why decentralization and scalability matter.

Then move on to Solidity Smart Contract Development. (5hrs)
Learn the syntax, understand how state and functions work, and get comfortable reading simple contracts. No prior coding experience is required.

You should also learn Basic Web3 Wallet Security. (1hrs)
Understanding how users sign transactions and how they lose funds will make you a better auditor later.

Now, the most important one of all - the Smart Contract Security course. (24hrs)
This introduces common vulnerabilities such as reentrancy, oracle manipulation, and access control issues, and it helps you start thinking like a security researcher. It will provides a solid foundation.

8. Step two: Practice Solidity, but do not get stuck
At this stage, you should write some simple contracts.
Build a basic token. Create a voting contract. Try a simple staking mechanism. These projects do not need to be impressive. Their purpose is to help you understand how real contracts behave. Deploy to a testnet. Interact with your contracts through a wallet. Send transactions. Break things on purpose. Observe what happens when inputs are wrong, when permissions are missing, or when assumptions fail.
Read transaction traces. Look at state changes. Try to reason about what an attacker could do if this contract held real value.
This hands-on interaction is where understanding actually forms. Reading code helps, but deploying, using, and breaking your own contracts is what makes the behavior stick in your head.
You should also read real protocol code. A good collection can be found here:
Do enough of these to feel comfortable navigating real contracts, then move on. Staying here too long is a common trap.
9. Step three: Level up your security knowledge even more
One resource is mandatory if you want to become a serious auditor.
Owen Thurm’s Web3 Security 101 playlist:
Watch all of it, it's GOLD🪙. Take notes. Revisit it later. The content is dense, practical, and extremely valuable. Treat it like you paid $10k for it.
10. Step four: Practice for real
Courses will not make you an auditor. Practice will.
Real learning begins when you start auditing real codebases. This usually happens through contests.
You will enter contests and feel completely lost. You will miss obvious bugs. Your first reports will be bad. Your brain will hurt.
That is exactly how it should be.
You can track active contests here:
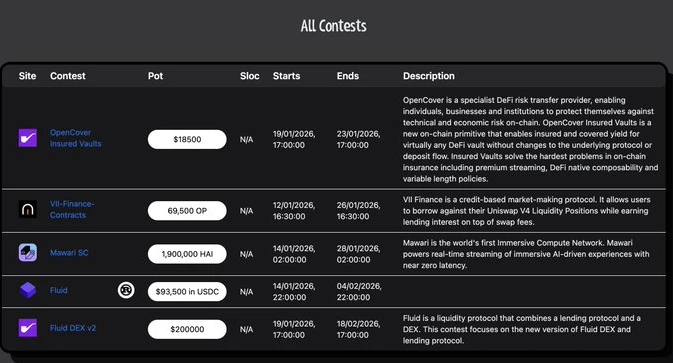
Security contests are valuable because they are permissionless. They allow you to prove your skills publicly.
BUT, they may not exist forever. Lately their count is declining fast. So use them while they are available.
If contests disappear, you still have options. Your alternatives will be:
- Finding live bugs on bug bounty platforms (even low or medium severity), where codebases are usually audited multiple times by top firms
- Finding bugs in live protocols that don’t have a bounty, reporting them privately, and using that work as proof later
- Deep writeups of protocols you audited solo
- Reproductions of real exploits with explanations
- Clear threat models of existing DeFi systems
Whatever you do, publish your work on GitHub. Firms will ask for it later.
11. Step five: Going professional
Once you have real proof of your skills, you can start monetizing.
At this point, you can choose one of three paths:
- Bug bounties – You hunt for vulnerabilities in live codebases and get paid when you find valid issues.
- Freelance audits – Web3 security firms hire freelance auditors for individual engagements, allowing you to earn per audit.
- Traditional firm – You work full-time with a single security firm and earn a fixed salary.
Not many firms hire junior auditors but some does as additional 3rd or 4th reviewers on audits. Try to contact all kinds of security firms when you already have some leverage.
Expect rejection. You will be ignored and turned down. That is normal.
What matters is the number of real value you have contributed to the space, the quality of your findings, and the clarity of your thinking. If you keep producing real work, opportunities will eventually appear.
12. Step six: Continuous improvement
Security is not something you “finish learning.” It's an ongoing process. You gotta be wiling to learn everyday and spend lots of hours in bettering your skills and knowledge. Improving yourself daily will open more doors for you.
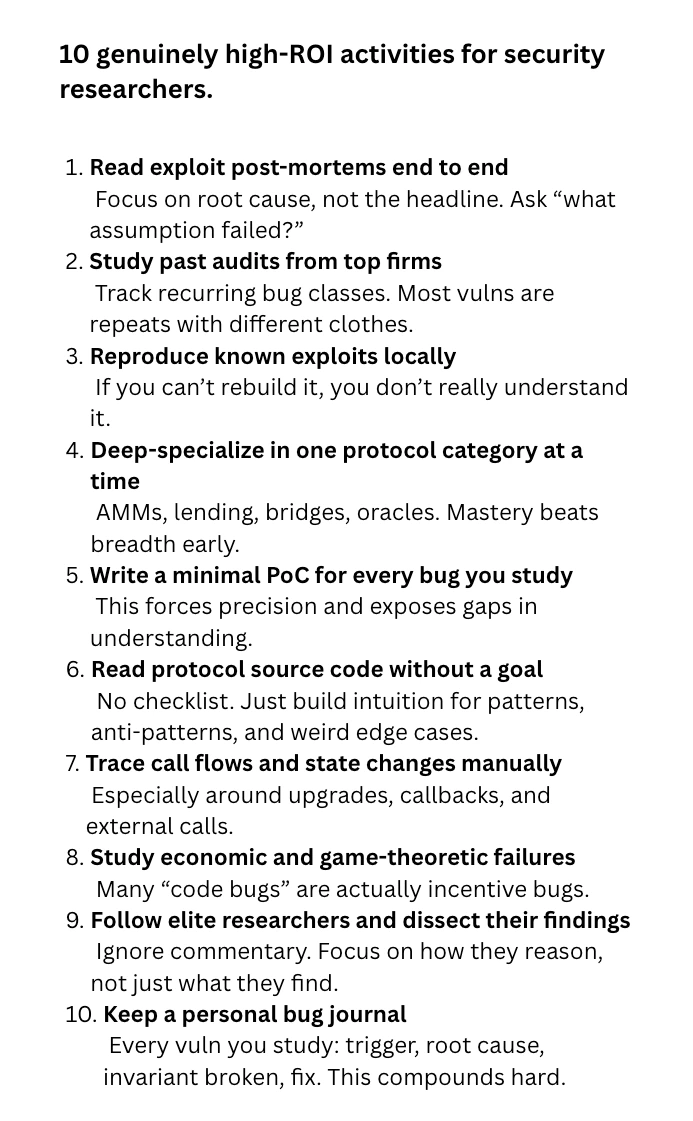
Most auditors waste time staying busy instead of getting better. Being busy does not make you dangerous. Here are 10 genuinely high-ROI activities. Do them as much as possible:
13. Here are our picks for the most valuable resources along the way
If you are serious, these are worth your time.
- Owen Thurm – Web3 Security 101 (YouTube)
- Past Audit Reports
- DeFi Research Base
- Blogs and books – mixbytes.io, rareskills.io, masteringethereum.xyz
- Deep Work
- Newsletter
- Past Hacks
- Beginners Telegram Community
- Awesome Smart Contracts
14. Conclusion
Web3 security is a long-term game. Progress is slow, mistakes are constant, and clarity comes late. Most people quit before that point.
If you keep practicing, publishing real work, and improving how you think, the field will eventually take you seriously. And we can guarantee you - it's WORTH it.
